# 3) DOM XSS in document.write sink using source location.search
the search term is included on the result page.
A simple XSS attempt fails:
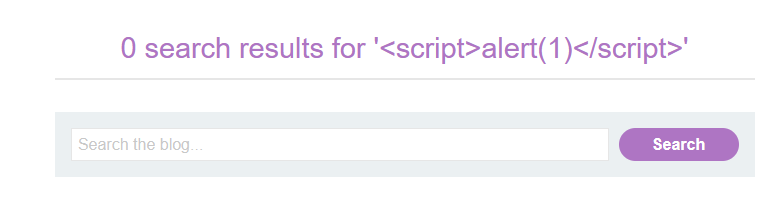
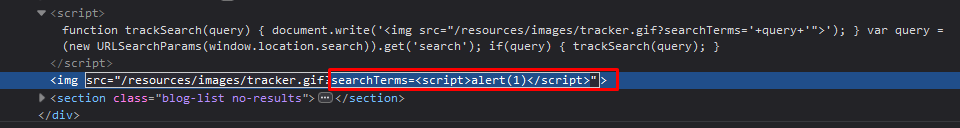
it shows that a javascript takes the search term out of the URL and writes it into an img-tag for some type of tracking:
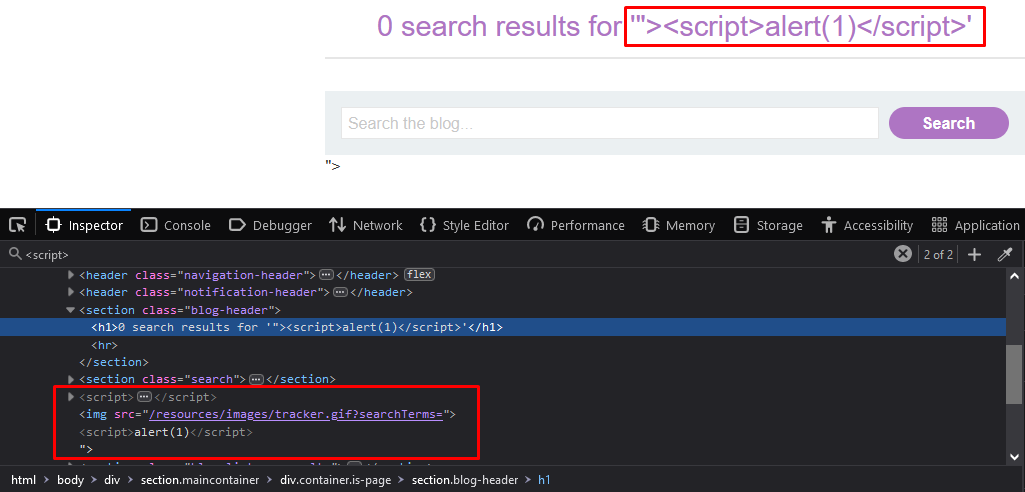
Using the browser tools, I can inspect the resulting HTML. It is visible that my search term is embedded without any apparent safeguards:
Of course, the script tags are within a string here, so they are harmless. However, if I can terminate the string by injecting double quotes, then I can manipulate the resulting HTML freely.
#### The malicious payload
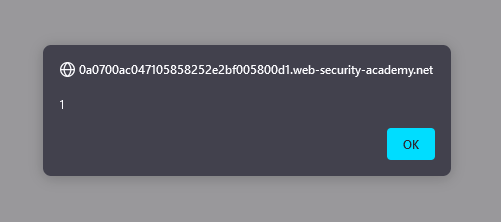
Injecting `">` results in the following HTML:
and we have solved the lab
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://sayonara.gitbook.io/writeups/portswigger/xss/3-dom-xss-in-document.write-sink-using-source-location.search.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.